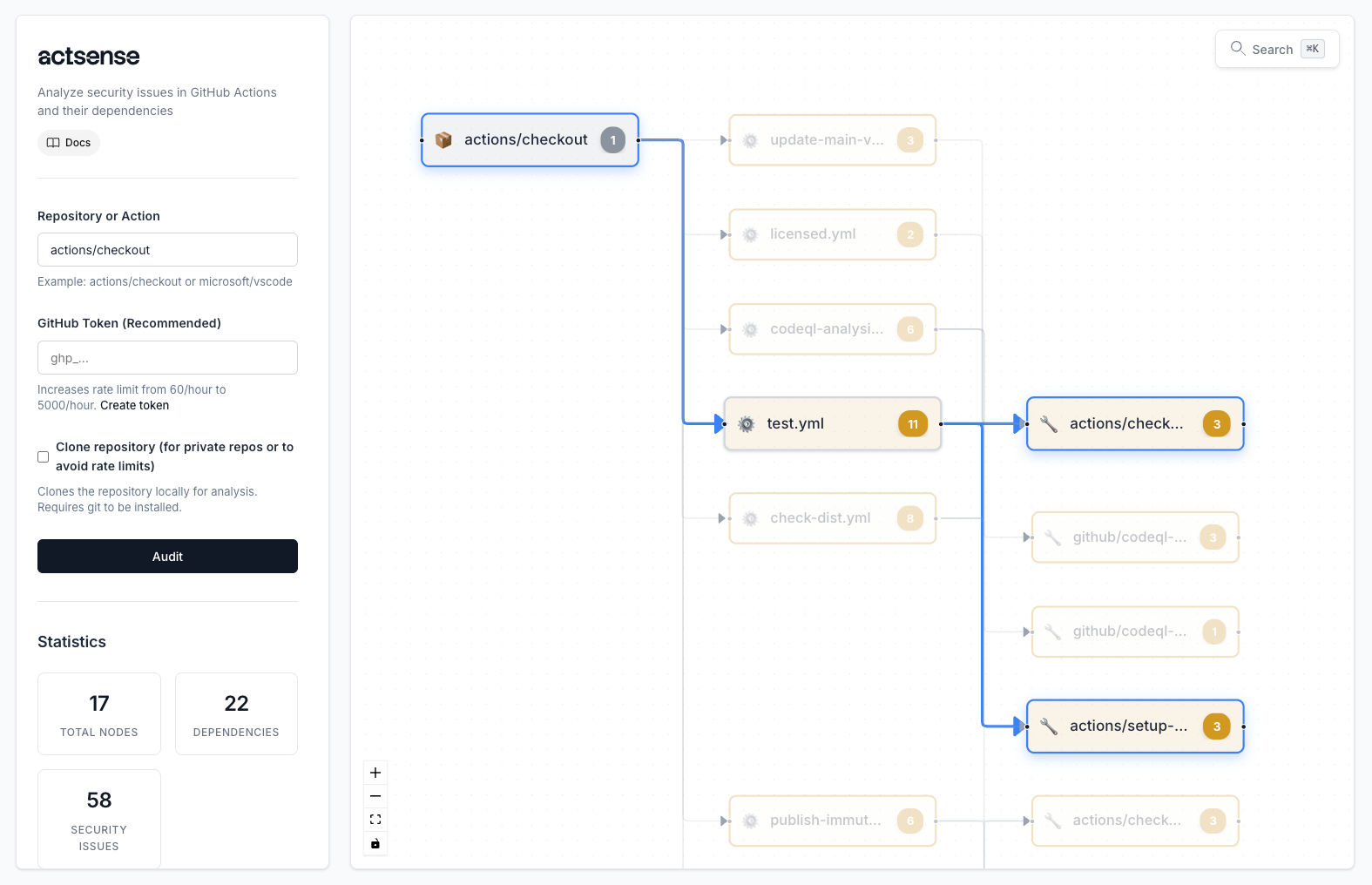
actsense
Comprehensive security auditing for GitHub Actions workflows. Detect vulnerabilities and exposures, analyze dependencies, and secure your CI/CD pipelines.
$ docker run --rm -p 8000:8000 ghcr.io/0xcardinal/actsense:latest
Why actsense?
GitHub Actions workflows can introduce serious security vulnerabilities and exposures. actsense helps you:
- Detect ~70 vulnerability and exposure patterns across workflows and dependencies
- Analyze action dependencies with interactive visual graphs
- Identify supply chain risks and exposures from untrusted or outdated actions
- Prevent credential exposure and permission escalation
Ready to secure your workflows? Explore our comprehensive vulnerability documentation with detailed explanations, evidence, and step-by-step mitigation strategies.
Vulnerability and Exposure Categories
- Unpinned or weak pinning checks (
unpinned_version,no_hash_pinning,short_hash_pinning) - Outdated or inconsistent versions (
older_action_version,inconsistent_action_version) - Untrusted and typosquatting exposure checks (
untrusted_action_source,typosquatting_action) - Unpinnable supply chain exposures (Docker/composite/JavaScript resource checks)
- Overly permissive token and job permissions (
overly_permissive,github_token_write_all) - Excessive write scope and escalation paths (
excessive_write_permissions,token_permission_escalation) - Cross-repository and branch protection bypass exposure checks
- Environment protection and deployment policy bypass risks
- Hardcoded secret and cloud credential detection (
potential_hardcoded_secret, cloud credential checks) - Secret exposure in environment and workflow runtime (
secret_in_environment,environment_with_secrets) - Optional secret input and insecure secret-handling exposures
- Long-term cloud credential exposures vs OIDC best practices
- Dangerous trigger and event exposure checks (
dangerous_event,insecure_pull_request_target) - Input and context injection checks (
unvalidated_workflow_input,code_injection_via_input) - Shell/script execution risks (
shell_injection,script_injection,risky_context_usage) - Malicious command patterns and obfuscation (
malicious_curl_pipe_bash,malicious_base64_decode,obfuscation_detection)
- Public self-hosted runner exposure checks (
self_hosted_runner_pr_exposure, issue exposure) - Secrets and write-all risk on self-hosted runners
- Runner label confusion and workload hijacking risks
- Network exposure and lateral movement risk detection